MITRE Frameworks Explained: The Defender’s Real-World Toolkit (ATT&CK, D3FEND, CAR, ENGAGE & More)
- DFIRHive

- Oct 23, 2025
- 9 min read

Why MITRE Still Matters (and Why It’s Not Just a Matrix)
Let’s be honest — we’ve all seen that big, colorful MITRE ATT&CK matrix and felt like we were supposed to memorize every technique ID.
But here’s the truth: MITRE isn’t a checklist — it’s a language.
When we spot a suspicious PowerShell activity, MITRE helps us to describe it precisely:
“That’s T1059.001 – Execution via PowerShell,” connected to “T1105 – Ingress Tool Transfer” for command-and-control delivery.
That shift — from “weird PowerShell” to a known technique — changes everything. It brings structure to the chaos.
MITRE helps analysts move beyond isolated alerts and start mapping attacker behavior chains — the sequence of actions that make up a real intrusion.
And MITRE goes beyond ATT&CK. The full ecosystem includes:
ATT&CK – Describes attacker tactics and techniques
CAR – Turns behaviors into detection logic
D3FEND – Maps defensive countermeasures
ENGAGE – Guides deception and active defense
CTID – Validates detections through real adversary simulations
All free, open, and community-tested.
A Quick Scenario Before We Dive Deep
Let's assume you are in a SOC. An alert fires — psexec.exe is being used for lateral movement.
You could dismiss it as noise — or, open MITRE ATT&CK and immediately see what’s happening:
Here’s what you’d find:
Technique: T1021.002 – SMB/Windows Admin Shares (under the Lateral Movement tactic)
Example Procedures: threat groups like APT29 and FIN6 have used PsExec in similar ways.
Detections: monitor for remote service creation, SMB traffic spikes, and Windows Event ID 7045.
Mitigations: restrict admin share access and limit privileged credentials.
That’s threat-informed defense in action — turning raw alerts into actionable understanding.
1. MITRE ATT&CK: The Universal Language of Adversary Behavior
Let’s start with the core — MITRE ATT&CK (Adversarial Tactics, Techniques, and Common Knowledge).
Back in 2013, MITRE researchers at Fort Meade ran controlled red-team exercises to document exactly how attackers operate. That experiment — known as the Fort Meade Experiment — became what we now recognize as the ATT&CK Framework.
Today, it’s the global reference used by blue teams, red teams, and threat-intel analysts alike.
Each ATT&CK entry explains:
Tactic – The goal (why) — e.g., Initial Access, Persistence, Exfiltration.
Technique – The how — e.g., Phishing, PowerShell Execution, Credential Dumping.
Procedure – The real-world example — how specific threat actors performed it.
Over time, ATT&CK expanded from Windows to macOS, Linux, mobile, and even ICS environments.
How to Use MITRE ATT&CK
Knowing what ATT&CK is matters, but the real skill is knowing how to use it inside your workflow.
Here’s a simple way to get started:
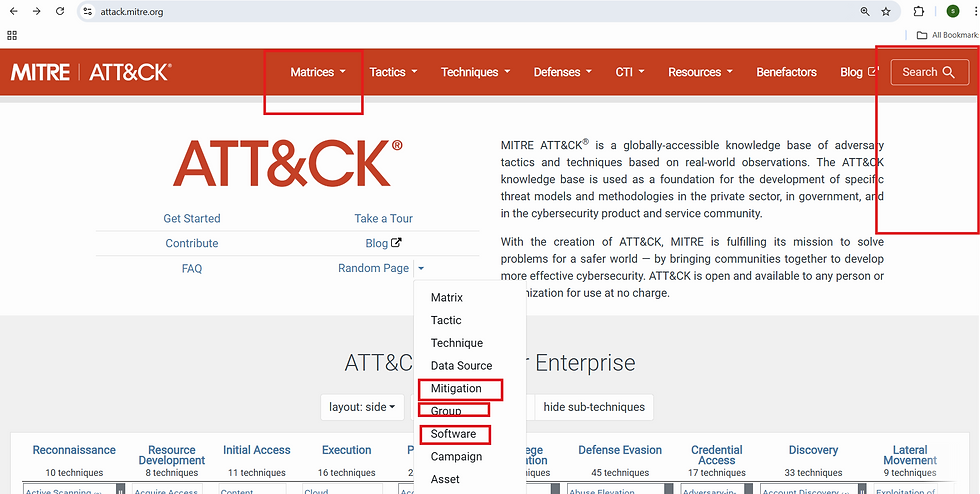
Start at the Source
Visit attack.mitre.org. This is the central hub — everything from tactics, techniques, sub-techniques, and real-world examples lives here.
You’ll find sections like:
Enterprise Matrix: For Windows, macOS, Linux, and more.
Groups: Lists of threat actors (e.g., APT29, FIN7) and their known techniques.
Software: Tools, malware, and scripts tied to ATT&CK IDs.
Mitigations: Defensive strategies for each technique.
Let's say, we are analyzing an alert or IOC, we can start by searching that behavior or process name here.
Example: Search “PowerShell” → and we’ll land on T1053→ Scheduled Task
That gives its full context — related techniques, actors, detections, and mitigations.

Alternative: ATT&CK Navigator
Go to ATT&CK Navigator. This tool helps visualize the coverage.
Think of it as your personal “detection heatmap.”
How to use it:
Import your own detection coverage (from SIEM, EDR, or playbooks).
Color-code techniques:
🟩 Detected
🟨 Partially Detected / Needs Testing
🟥 Blind Spot
Share that map across your blue, red, and threat intel teams.

Correlate Behavior During Investigations
During an IR case or threat hunt, use ATT&CK as the behavioral map:
Look into suspicious activity (e.g., registry modification, scheduled task).
Search each one in MITRE.
Link them together as a sequence of tactics — like Execution → Persistence → Privilege Escalation.

Pivot from ATT&CK to Detection & Defense
Once you’ve identified what the attacker did, the next step is learning how to detect in your environment and prevent it — that’s where MITRE CAR and D3FEND come in.”
Go to CAR.mitre.org → find ready-made analytics.
Go to D3FEND.mitre.org → explore mapped defenses.
2. MITRE CAR: Turning Behavior into Detection Logic
MITRE’s Cyber Analytics Repository (CAR) turns theory into practice.
Where ATT&CK tells you what to look for, CAR tells you how to look for it.
Each CAR analytic includes:
A mapped ATT&CK technique
Logic or pseudocode for detection
Example queries (Splunk, Elastic, Sigma, etc.)
Detection rationale and false positive notes
That’s a starting point. You can then enrich it with parent process checks, frequency rules, or EDR telemetry.
How to Actually Use MITRE CAR
Let’s go step by step:
Start at CAR.mitre.org
Head to CAR.mitre.org and open the Analytics section. Here we'll see detection analytics mapped directly to ATT&CK techniques.
Here we can:
Search by ATT&CK ID (e.g., T1053, T1047).
Filter by platform (Windows, Linux, etc.).
Explore detections by data source (Sysmon, Event Logs, PowerShell, Network).
Finding the Analytic for the Technique
In our case, we’ll look at T1053 — Scheduled Task/Job .
When we search “T1053” inside CAR, we’ll see several mapped detections — including:
CAR-2013-08-001 – Execution with schtasks
CAR-2020-09-001 – Scheduled Task FileAccess
CAR-2021-12-001 – Suspicious Scheduled Task Creation or Modification

Understanding the Detection Logic
Let’s look at a real example from CAR-2013-08-001 – Execution with schtasks.
Each entry gives information, which includes:
The technique ID & title
A summary of the behavior it detects
Sample queries and logic snippets
Detection notes to refine tuning

_fetch * from event where $LogName=WINDOWS-SYSMON AND $EventID=1 AND $App=schtasks.exe AND $Process=regex(.*(\/create|\/run|\/query|\/delete|\/change|\/end).*)i limit 100
What this command does:
This analytic detects suspicious command-line executions of schtasks.exe, the Windows Task Scheduler CLI tool.
By flagging these parameters in process creation logs, we can quickly identify persistence or execution attempts that blend in with system activity.
Map It Back to ATT&CK
Each CAR analytic is tied to one or more ATT&CK techniques. In this case:
CAR Analytic | ATT&CK Technique | Tactic |
CAR-2013-08-001 | T1053.005 – Scheduled Task/Job | Persistence / Privilege Escalation |
So, if we’ve already mapped suspicious task activity under ATT&CK, CAR provides a ready-made detection query to validate the coverage — no guesswork needed.
Note:
CAR detections are templates, not drop-in rules.
Always adapt them to your log format, field names, and local baseline — that’s how we move from generic logic to environment-specific intelligence.3. MITRE D3FEND: The Defensive Counterpart
If ATT&CK describes the offense, D3FEND is the defense’s playbook.
Funded by the NSA, D3FEND is a knowledge graph that maps security controls and mitigations directly to ATT&CK techniques.
Example Use: If ATT&CK says attackers are abusing PowerShell, D3FEND might guide you to implement “Script Execution Prevention” or “Process Command-Line Auditing.”
How to Use D3FEND (Step-by-Step)
Start at the Source
Visit d3fend.mitre.org. You’ll see an interactive graph connecting ATT&CK techniques with defensive countermeasures.
Search for the technique you’re investigating (e.g., T1053.005 – Scheduled Task/Job).
D3FEND will highlight which defensive techniques mitigate that attack — like File Monitoring, Execution Prevention, or Process Command-Line Auditing.

Pick the Right Defensive Techniques
Each D3FEND entry is actionable — it tells us what to implement and why.
Here’s what we’ll typically find:
Definition: What this defense does (e.g., monitors script execution).
Mapped ATT&CK Techniques: Which attacks it stops or mitigates.
Implementation Tips: System controls, configurations, or detection aids.

Combine with ATT&CK & CAR
Use ATT&CK, CAR, and D3FEND together.
So for this scenario:
ATT&CK says: “Attackers run PowerShell (T1059.001).”
CAR says: “Detect PowerShell execution via Sysmon Event ID 1.”
D3FEND says: “Prevent it with Script Execution Prevention and Logging Policies.”
"Use D3FEND when you’re planning hardening or mitigation strategies after incident response."
4. MITRE ENGAGE: Taking the Fight to the Adversary
MITRE ENGAGE is all about active defense — going beyond monitoring and detection.
What Is MITRE ENGAGE?
MITRE ENGAGE is a framework for Active Defense and Adversary Engagement. It gives blue teams structured ways to:
It’s structured into five phases:
Prepare – Define goals, risks, and engagement assets.
Expose – Place traps or decoys (fake accounts, fake shares).
Affect – Mislead or frustrate attackers.
Elicit – Observe how they behave.
Understand – Analyze their actions to improve defenses.
Example: We deploy fake database credentials that lead to a monitored honeypot. An attacker uses them → Now we can log IP, tools, and sequence → We learn while they waste time.
ENGAGE gives a language and method for that strategy — safely and legally.
ENGAGE Matrix — A Quick Guide
Open the matrix
URL: https://engage.mitre.org/matrix/ → choose Enterprise.
What we see: a grid of phase columns (Prepare → Expose → Affect → Elicit → Understand)

Filter by your ATT&CK technique
In the filter bar, type the ATT&CK ID — for this case, T1053 (Scheduled Task/Job).
The matrix now highlights relevant ENGAGE techniques connected to this behavior — for example:
System Activity Monitoring (Expose)
Lures (Affect/Elicit)
Software Manipulation (Disrupt)
These represent actions we can take to study or contain adversary activity linked to scheduled tasks or PowerShell persistence.

Click a highlighted tile
When we click a tile like “Lures”, we will get an in-depth description —
Definition
Deceptive systems and artifacts intended to serve as decoys, breadcrumbs, or bait to elicit a specific response from the adversary.
This tells that Lures are defensive tricks — fake credentials, bogus scripts, or files like update.ps1 — designed to tempt an attacker into interacting.
What can be done Practically:
Place fake PowerShell scripts in shared directories or decoy hosts (e.g., update.ps1).
Embed dummy credentials or “admin-looking” task files that appear legitimate.
Log every access or execution attempt using Sysmon and Windows Security 4688/4698 events.
When the attacker takes the bait — we can get data: command lines, IPs, timestamps, and the attacker’s toolchain.

"ENGAGE turns the network from a static environment into an intelligence sensor."
5. CTID & ATT&CK Emulation Plans — Test What You Know
MITRE’s Center for Threat-Informed Defense (CTID) publishes detailed Adversary Emulation Plans.
"Once we’ve mapped and defended behaviors, CTID lets to test whether the detections truly work — by simulating real adversary activity.”
“CTID’s emulation plans are an essential part of threat-informed defense — helping defenders validate detection coverage through red team-style simulations.”
How to Emulate:
And, we’ll land on: a list of adversary profiles and emulation topics (searchable).
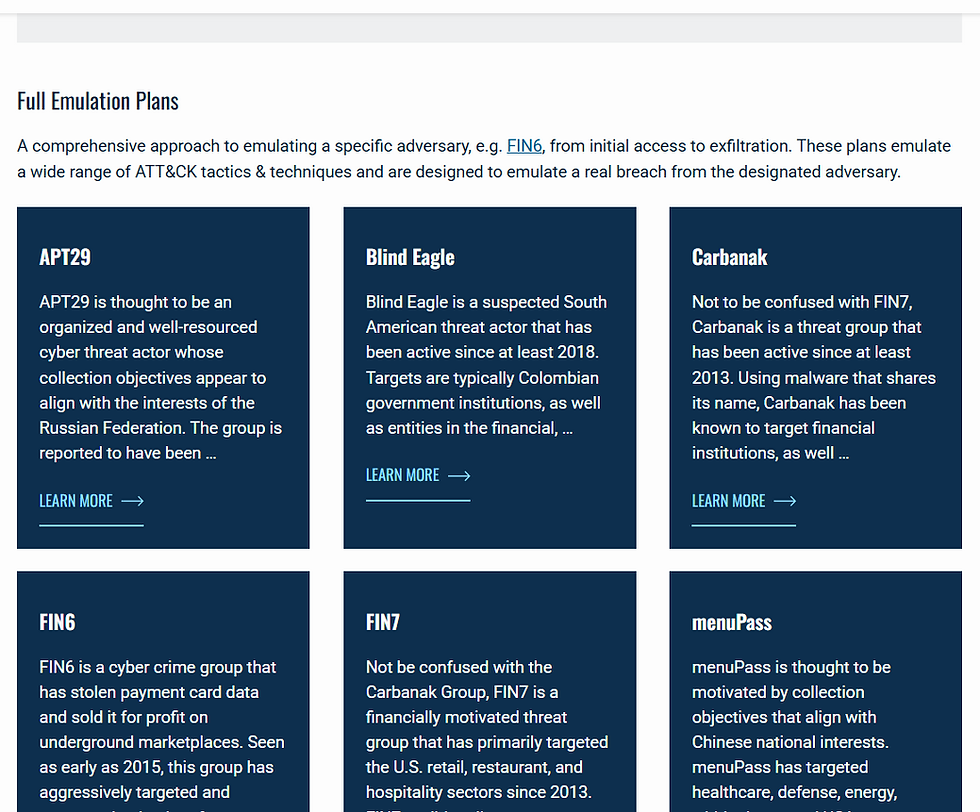
"MITRE CTID hosts detailed adversary emulation plans mapped to real threat groups."
Let's now find the adversary and actor: When we explore the ATT&CK framework, we’ll be able to find groups of APTs linked to specific behaviors. The one matching your activity or most relevant to your environment is your starting point.

Open the most relevant plan in emulation library: Click the plan with a title that matches your need (e.g., APT 13, APT29).
What you are going to see: overview, preconditions, step-by-step actions (often numbered), and attachments (scripts/commands).
Now, run these in a lab to verify if your alerts fire when they should. It’s like a red team exercise, but reproducible and based on reality.

Stuff Worth Bookmarking
MITRE ATT&CK — for building coverage maps
CAR Analytics Library — for detection inspiration
MITRE D3FEND — for mapping defenses
MITRE ENGAGE — for active defense ideas
Emulation Library — for real attacker scenarios
Quick Reference: MITRE Ecosystem in One View
Phase | Goal | Framework | Outcome |
Threat Understanding | Know what attackers do | ATT&CK | Map tactics & techniques |
Detection Building | Find behavior in logs | CAR | Create detections |
Defensive Design | Strengthen controls | D3FEND | Apply countermeasures |
Active Defense | Observe & mislead | ENGAGE | Deception operations |
Validation | Test readiness | CTID/AEP | Validate coverage |
MITRE Has Its Quirks
Like every framework, MITRE has limits — and it’s okay to say that.
Too big to memorize: No one knows every ID, and it is complicated at first
Not plug-and-play: CAR analytics are examples, not production-ready. Always tune.
Lagging updates: ATT&CK doesn’t always reflect the latest TTPs — threat actors evolve faster.
Detection ≠ Prevention: D3FEND (still in beta) helps, but operationalizing it takes effort.
The point isn’t perfection — it’s direction. MITRE gives defenders a shared language, even if the dictionary is still growing.
Conclusion
MITRE doesn’t replace experience — it organizes it. It helps to see where an alert fits in the bigger picture, and what to do next.
So the next time if you spot a suspicious PowerShell or scheduled task, don’t overthink it. Look it up, map it, detect it, and fix what’s missing.
That’s not theory — that’s how threat-informed defense looks in real life.


Comments